What Guideline M Actually Means (In Plain English)
Guideline M is the part of the security clearance system that deals with the misuse of computers, networks, information systems, digital devices, and workplace technology.
At its core, Guideline M asks:
👉 Can this person be trusted to follow technology, cybersecurity, and information-system rules when handling sensitive systems or data?
That sounds simple.
But in practice, Guideline M can become one of the most dangerous and misunderstood guidelines in the entire security clearance process.
Many applicants assume this guideline only applies to:
- hackers
- cybercriminals
- classified network intrusions
- espionage-level misconduct
That is not true.
At National Security Law Firm, our security clearance lawyers have represented clients facing Guideline M concerns involving:
- workplace computer misuse
- unauthorized software downloads
- pornography on government systems
- excessive personal browsing
- prohibited cloud storage usage
- improper USB or external media use
- unauthorized AI tool usage
- cybersecurity policy violations
- remote work system mistakes
- improper access to databases or files
Many of these people never imagined they were creating a security clearance issue.
That is what makes Guideline M so dangerous.
The concern is often not:
👉 “Was this criminal?”
The concern is:
👉 “Does this conduct suggest poor judgment, unreliability, recklessness, or unwillingness to follow security rules?”
That distinction is critical.
Because many Guideline M cases involve conduct that:
- was common in the workplace
- was normalized by coworkers
- did not involve classified information
- did not lead to criminal charges
- or was never intended to cause harm
And yet:
👉 those same actions can still trigger suspension, denial, or revocation of a security clearance.
Quick Answer: Can IT Misuse Affect Your Security Clearance?
Yes—absolutely.
Guideline M can affect your security clearance if the government believes your misuse of computers, information systems, or digital technology raises concerns about:
- judgment
- reliability
- trustworthiness
- cybersecurity discipline
- or willingness to follow rules
The government does not only evaluate:
👉 what happened
It evaluates:
👉 what your conduct suggests about future risk.
That means relatively ordinary workplace behavior can sometimes become a serious clearance issue.
Examples include:
- using unauthorized software
- browsing prohibited content on work devices
- transferring files improperly
- using personal cloud storage for work material
- plugging unauthorized USB devices into systems
- bypassing IT restrictions
- sharing passwords
- unauthorized AI tool use involving government data
Many Guideline M concerns begin with something that initially seems small.
Then:
- system logs are reviewed
- investigators ask questions
- explanations become inconsistent
- and the issue escalates
That escalation is what destroys many cases.
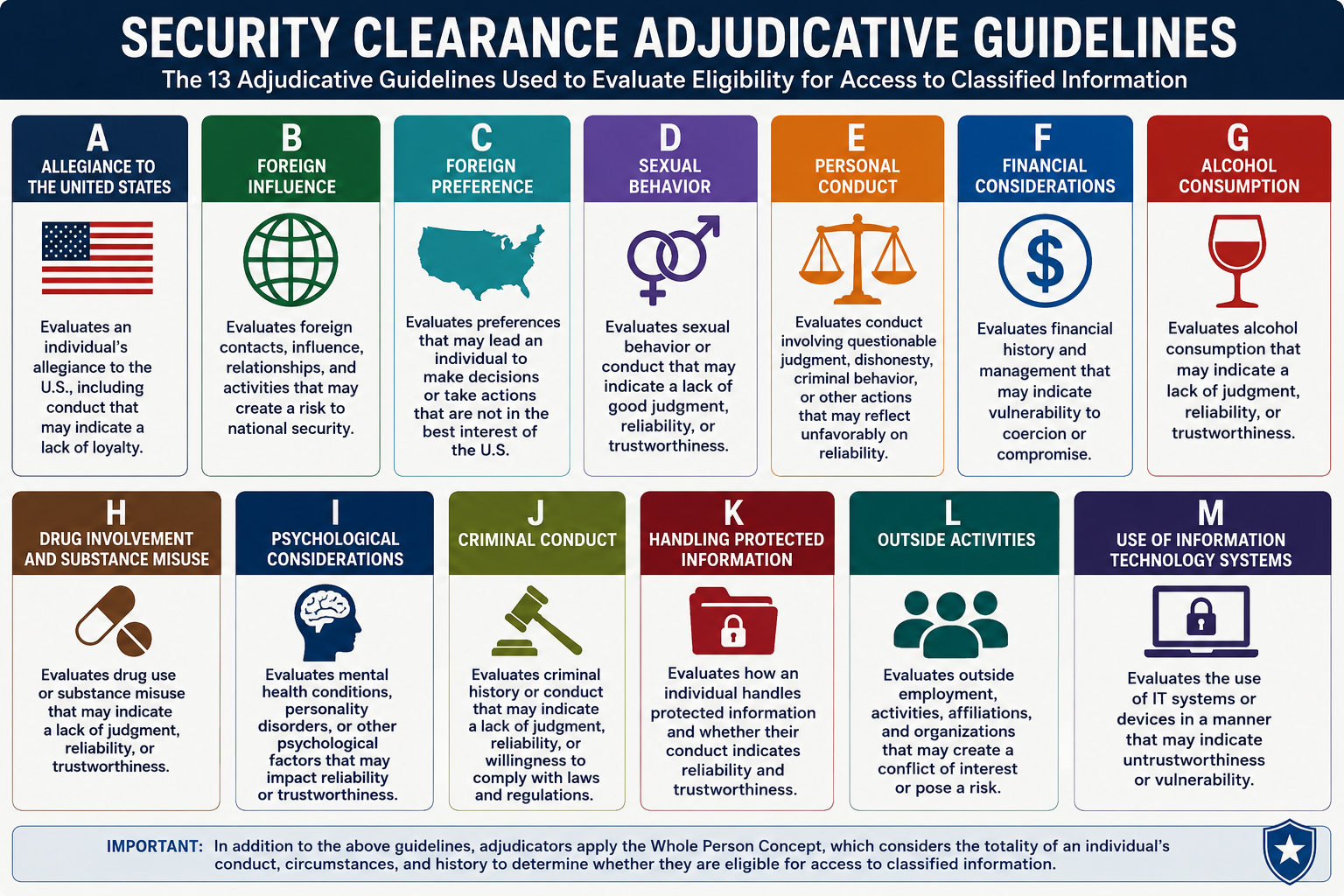
To understand how Guideline M fits into the broader adjudicative framework, review the
👉 Security Clearance Adjudicative Guidelines
Why Guideline M Cases Are So Misunderstood
Guideline M is misunderstood because most people think about computer misuse in criminal terms.
They assume:
- “I didn’t hack anything.”
- “Everyone used the work computer that way.”
- “It wasn’t classified.”
- “I didn’t know the rule.”
- “I wasn’t trying to do anything wrong.”
But security clearance law does not operate like criminal law.
Adjudicators are not only evaluating:
👉 whether you committed a crime.
They are evaluating:
👉 whether your conduct creates risk.
That means conduct can still become a major security clearance problem even when:
- no criminal law was violated
- no classified data was exposed
- no discipline initially occurred
- or coworkers engaged in similar behavior
This is one of the hardest parts for applicants to understand emotionally.
Because many Guideline M cases feel:
👉 arbitrary
👉 selective
👉 or unfair
Especially when:
- others engaged in similar conduct
- workplace culture normalized the behavior
- or enforcement was inconsistent
But adjudicators are not evaluating workplace fairness.
They are evaluating:
👉 whether your conduct reflects the level of judgment expected from someone entrusted with access to sensitive systems or classified information.
Why Guideline M Cases Feel So Dangerous
Unlike some other guidelines, Guideline M cases often escalate suddenly.
One day everything feels normal.
Then:
- an IT audit occurs
- logs are reviewed
- cybersecurity personnel become involved
- or a workplace investigation begins
Applicants often discover there is already a detailed record showing:
- websites visited
- downloads performed
- login history
- file transfers
- external device usage
- cloud activity
- messaging applications
- or network behavior
That realization creates panic.
Especially because many people immediately begin worrying about:
- browser history
- pornography allegations
- AI usage
- work-from-home behavior
- remote device usage
- deleted activity
- or old policy violations
And once a cybersecurity or insider-threat investigation begins:
👉 the issue can escalate very quickly.
This is one reason Guideline M cases often overlap with:
👉 Guideline E – Personal Conduct
Because credibility, disclosure, and honesty frequently become part of the analysis.
Why the Insider Perspective Matters in Guideline M Cases
Most online discussions about Guideline M focus only on:
- the technical conduct
- the IT rule
- or the workplace policy
But that is not how adjudicators actually decide these cases.
At National Security Law Firm, our team includes attorneys who understand how national security decision-makers evaluate:
- cybersecurity discipline
- insider-threat concerns
- technology misuse
- and risk behavior patterns
That matters because Guideline M cases are rarely about the isolated technical act itself.
They are about what the act suggests.
For example:
A single unauthorized download might seem minor.
But to an adjudicator, it can suggest:
- disregard for rules
- willingness to bypass controls
- poor judgment under pressure
- or future cybersecurity risk
That interpretation process is what most applicants fail to understand.
And it is why many people accidentally make their case worse while trying to explain themselves.
What This Guide Will Help You Understand
If you are facing a Guideline M concern—or worried about one—this guide will explain:
- what actually triggers Guideline M issues
- how adjudicators evaluate IT misuse
- which types of computer activity create the most concern
- how workplace investigations escalate into clearance actions
- what strong mitigation actually looks like
- and how successful applicants resolve these concerns before denial occurs
Most importantly:
👉 this guide will help you understand how the government interprets technology misuse from a security-risk perspective.
Because until you understand that:
👉 you are reacting emotionally instead of strategically.
When Guideline M Actually Comes Up in Real Cases
Guideline M issues appear in far more situations than most people realize.
Some are serious.
Others begin with ordinary workplace behavior that unexpectedly escalates.
The most common categories include:
Improper Use of Government or Workplace Computers
This is one of the largest categories under Guideline M.
Examples include:
- excessive personal internet use
- prohibited browsing activity
- streaming or gaming on work systems
- using systems for unauthorized personal projects
- violating acceptable use policies
Many applicants are shocked when this becomes a clearance issue.
Especially because they may have seen coworkers engage in similar conduct.
But adjudicators often interpret repeated policy violations as:
👉 willingness to disregard security rules when convenient.
Unauthorized Software or Downloads
This includes:
- installing unapproved applications
- downloading prohibited programs
- using unauthorized browser extensions
- bypassing software restrictions
- using unapproved productivity or AI tools
This category has become increasingly important in modern clearance cases because agencies are aggressively evaluating:
👉 cybersecurity discipline.
Unauthorized AI Tool Usage
This is becoming one of the fastest-growing Guideline M concerns.
Examples include:
- uploading work-related material into AI systems
- using ChatGPT or external AI tools against policy
- processing government-related information through unauthorized platforms
- storing agency data in AI-integrated systems
Many applicants assume:
👉 “It wasn’t classified, so it doesn’t matter.”
But adjudicators increasingly view unauthorized AI usage as a:
👉 judgment and policy-compliance issue.
Improper USB or External Device Use
This includes:
- plugging unauthorized devices into systems
- transferring files improperly
- bypassing removable-media restrictions
- using personal drives on secure systems
Even isolated incidents can trigger scrutiny because removable media creates:
👉 exfiltration and insider-threat concerns.
What the Government Is Actually Worried About
To understand Guideline M, you have to stop thinking about the issue as:
👉 “computer misuse”
and start thinking about it as:
👉 trust and cybersecurity discipline
That is how adjudicators evaluate these cases.
The government is not only asking:
👉 “What did this person do?”
It is asking:
👉 “What does this conduct suggest about how this person handles rules, systems, and risk?”
That concern usually falls into several categories.
1. Judgment Problems
Many Guideline M cases are fundamentally about judgment.
Adjudicators evaluate questions like:
- Did the applicant knowingly violate policy?
- Did they prioritize convenience over rules?
- Did they exercise poor digital judgment?
- Did they ignore obvious risks?
Even relatively minor violations can create concern if they suggest:
👉 a pattern of careless decision-making.
2. Willingness to Follow Security Rules
This is one of the biggest themes in Guideline M.
The government expects cleared personnel to follow security procedures precisely.
That means adjudicators are heavily focused on:
- policy compliance
- respect for restrictions
- cybersecurity awareness
- willingness to follow rules even when inconvenient
This is why applicants often get into trouble by saying things like:
- “Everyone did it.”
- “Nobody enforced the policy.”
- “It wasn’t a big deal.”
Those explanations usually make the case worse.
Because they suggest:
👉 normalization of noncompliance.
3. Insider Threat Concerns
This is one of the most serious aspects of Guideline M.
The government is increasingly focused on insider-threat prevention.
That means adjudicators evaluate whether conduct suggests:
- recklessness
- intentional circumvention
- disregard for system security
- or potential future misuse
Even if no classified information was compromised:
👉 behavior that resembles insider-threat patterns creates significant concern.
4. Cybersecurity Discipline
Modern security clearance systems place enormous emphasis on cybersecurity behavior.
Adjudicators increasingly evaluate:
- password discipline
- remote-work compliance
- unauthorized software use
- cloud storage behavior
- AI usage
- data transfer practices
- and digital hygiene generally
This is why Guideline M cases are becoming more common.
Many people still think:
👉 “This was just an IT policy issue.”
But agencies increasingly view poor cybersecurity behavior as:
👉 a national security issue.
5. Concealment or Dishonesty
Like many guidelines, Guideline M becomes significantly more dangerous when:
- explanations change
- evidence conflicts with statements
- logs contradict disclosures
- or applicants appear evasive
At that point:
👉 the case often expands into credibility problems.
And credibility issues frequently become more damaging than the original conduct.
The Guideline M Statute (Full Text)
The full statutory language for Guideline M can be reviewed here:
👉 Guideline M — Misuse of Information Technology Systems (Full Text)
But understanding the text alone is not enough.
The statute explains:
- what types of conduct can raise concern
- what mitigating conditions exist
- and how information technology misuse is categorized
What it does not explain is:
👉 how adjudicators actually apply those standards in real cases.
That is where strategy, mitigation, credibility, and record construction become critical.
How Adjudicators Actually Evaluate Guideline M Cases
This is where insider perspective matters most.
Adjudicators do not simply evaluate whether a technical violation occurred.
They evaluate:
👉 what the violation says about the person.
That distinction is critical.
Intent vs. Negligence
One of the first questions adjudicators ask is:
👉 “Was this intentional?”
Intentional conduct is generally viewed much more harshly than accidental or negligent conduct.
Examples of intentional conduct include:
- knowingly bypassing restrictions
- deliberately installing prohibited software
- intentionally accessing unauthorized systems
- using prohibited services after warnings were issued
Examples of negligent conduct might include:
- misunderstanding policy
- accidental misuse
- isolated mistakes
- inadvertent violations
But this is important:
👉 repeated negligence can still become disqualifying.
Because repeated negligence suggests:
👉 unreliable judgment.
Isolated Incident vs. Pattern
This distinction matters enormously.
An isolated mistake is often mitigable.
A repeated pattern of violations is much harder.
Adjudicators evaluate:
- how often the conduct occurred
- whether prior warnings existed
- whether the applicant corrected behavior
- and whether similar issues continued over time
The more normalized the behavior became:
👉 the harder mitigation becomes.
Sophistication of the Conduct
Another major factor is sophistication.
A minor accidental violation is very different from:
- deliberate circumvention
- technical concealment
- sophisticated unauthorized access
- intentional system manipulation
The more sophisticated the behavior appears:
👉 the more difficult the case becomes.
Because sophisticated conduct suggests:
- awareness
- planning
- and intentionality.
What the Logs Show
This is one of the biggest shocks for applicants.
Many Guideline M cases involve:
- audit trails
- login records
- browser history
- transfer logs
- security alerts
- monitoring reports
Applicants often assume:
👉 “I can just explain this later.”
But once logs exist:
👉 explanations must align with the evidence.
If they do not:
👉 credibility problems emerge immediately.
The “Paper Risk” Problem in Guideline M Cases
This is one of the most important concepts in clearance law.
Even when the technical conduct itself is relatively manageable…
👉 the way it appears in the record can still create denial risk.
This is what we call:
👉 paper risk
Examples include:
- vague explanations
- changing timelines
- incomplete admissions
- contradictions between logs and statements
- unclear descriptions of software or activity
Once the record feels:
- confusing
- inconsistent
- or evasive
👉 adjudicators become uncomfortable approving the file.
Pornography and Inappropriate Content on Government Systems
This is one of the most common—but least openly discussed—Guideline M categories.
Applicants are often shocked when pornography-related issues become security clearance problems.
But adjudicators are not evaluating morality.
They are evaluating:
- policy compliance
- judgment
- willingness to follow restrictions
- misuse of government systems
Examples include:
- viewing pornography on work devices
- accessing prohibited websites
- storing inappropriate material on systems
- violating workplace internet-use policies
These cases become especially dangerous when applicants:
- minimize the behavior
- deny obvious evidence
- or treat the issue casually
Because adjudicators often interpret that reaction as:
👉 lack of insight into the seriousness of the conduct.
Cloud Storage, Messaging Apps, and Modern Technology Risks
This is one of the fastest-growing areas under Guideline M.
Modern cases increasingly involve:
- Dropbox
- Google Drive
- personal cloud storage
- Signal
- Telegram
- unauthorized productivity platforms
- AI systems like ChatGPT
The concern is usually not the app itself.
The concern is:
👉 whether sensitive or work-related information was handled outside approved systems.
This becomes especially serious when applicants:
- move files for convenience
- bypass official systems
- or use personal technology without authorization
Again:
👉 convenience-based violations still create risk.
Remote Work and Home Network Issues
Remote work dramatically expanded Guideline M exposure.
Common issues include:
- unauthorized home devices
- unsecured Wi-Fi usage
- family access to work systems
- remote file transfer problems
- use of personal email or storage platforms
Many applicants developed informal habits during remote work periods that later became:
👉 documented security concerns.
What Raises Serious Concern Under Guideline M
Certain factors significantly increase risk under this guideline.
These include:
- intentional circumvention of rules
- repeated violations
- misuse after warnings
- concealment
- unauthorized classified access
- use of prohibited external devices
- unauthorized cloud storage
- insider-threat indicators
- attempts to hide or delete evidence
The more the conduct suggests:
👉 intentional disregard for security rules
the harder the case becomes to mitigate.
Why Some Guideline M Cases Feel Disproportionate
Many applicants feel blindsided because:
- the conduct was common in the workplace
- coworkers engaged in similar behavior
- the issue initially seemed minor
- or no one warned them earlier
That frustration is understandable.
But security clearance law is not evaluating:
👉 workplace fairness.
It is evaluating:
👉 whether the conduct creates national security risk.
That distinction is why these cases often feel so different from ordinary HR or disciplinary matters.
The Biggest Mistake People Make Under Guideline M
The biggest mistake is:
👉 treating the issue casually.
Applicants often say:
- “It was just browsing.”
- “Everyone used the system that way.”
- “I didn’t think it mattered.”
But to adjudicators, those statements often suggest:
👉 the applicant still does not understand the seriousness of the issue.
And if the applicant does not recognize the risk:
👉 the adjudicator worries the conduct could happen again.
What Strong Mitigation Actually Looks Like
Strong Guideline M mitigation usually includes:
- acknowledgment of the issue
- credible explanation
- acceptance of responsibility
- no repeat behavior
- evidence of retraining or remediation
- strong subsequent compliance
- consistency across all explanations
Most importantly:
👉 the applicant demonstrates understanding of why the conduct created concern.
How Guideline M IT Misuse Concerns Are Actually Mitigated
Many applicants assume that once computer misuse or cybersecurity concerns appear, their clearance is effectively over.
That is not true.
In reality, many Guideline M cases are highly mitigable when the issue is handled strategically and the record is built correctly.
The key is understanding what adjudicators are actually evaluating:
👉 judgment
👉 cybersecurity compliance
👉 browser-history and digital-conduct issues
👉 misuse of government systems
👉 credibility
👉 and whether the conduct still creates unresolved future security risk
Strong mitigation often involves:
- stopping the conduct immediately
- fully and consistently disclosing the issue
- avoiding panic-driven deletion or concealment
- demonstrating strong future compliance
- clarifying lack of malicious intent where appropriate
- and proving the conduct is unlikely to recur
For a deeper breakdown of what actually helps—and hurts—Guideline M cases, including browser-history issues, pornography on government computers, unauthorized downloads, cloud-storage misuse, cybersecurity-policy violations, and forensic-evidence concerns, review:
👉 How to Mitigate a Guideline M Security Clearance Concern
Advanced Strategy: How to Actually Beat a Guideline M Concern
Most applicants instinctively approach Guideline M the wrong way.
They focus on proving:
👉 “I wasn’t trying to do anything bad.”
But intent alone rarely resolves the issue.
Because adjudicators are not only evaluating:
👉 whether harm occurred.
They are evaluating:
👉 whether your conduct suggests future security risk.
That means the strongest Guideline M cases are built around:
- judgment
- reliability
- remediation
- cybersecurity discipline
- and credibility
—not simply lack of malicious intent.
Strategy Shift #1: Stop Treating the Issue Like a Technicality
One of the biggest mistakes applicants make is minimizing the conduct.
They say things like:
- “It was just a work computer.”
- “Everyone did it.”
- “I only checked it briefly.”
- “Nothing classified was involved.”
Those explanations often backfire.
Because they suggest:
👉 the applicant still does not understand why the conduct matters.
Strong cases acknowledge the concern directly.
Weak cases try to dismiss it.
Strategy Shift #2: Focus on Security Judgment, Not Innocence
Many applicants think the goal is proving they are innocent.
That is not the real objective.
The real objective is demonstrating:
👉 reliable future behavior.
This is why mitigation often focuses heavily on:
- retraining
- policy compliance afterward
- changed behavior
- acceptance of responsibility
- cybersecurity awareness
Adjudicators want confidence that:
👉 the problem will not happen again.
Strategy Shift #3: Understand That Logs Usually Win
Guideline M cases are often evidence-heavy.
That means:
- login records
- browser logs
- audit trails
- transfer histories
- security monitoring reports
frequently become central evidence.
This is dangerous because applicants sometimes:
- guess at timelines
- minimize conduct
- forget details
- or deny activity that is already documented
Once that happens:
👉 the issue shifts from IT misuse to credibility collapse.
And credibility problems are often harder to mitigate than the underlying conduct itself.
Strategy Shift #4: Avoid “Over-Explaining”
This is one of the most common mistakes in Guideline M cases.
Applicants panic and begin providing:
- excessive detail
- long emotional explanations
- unnecessary technical descriptions
- speculative statements
Instead of helping:
👉 this often creates contradictions.
The strongest responses are usually:
- focused
- controlled
- factually consistent
- and strategically framed
More information does not automatically improve the case.
Sometimes:
👉 it creates additional risk.
Strategy Shift #5: Align With Adjudicator Thinking
The strongest cases are built around this question:
👉 “What does the adjudicator need to see to feel comfortable approving this file?”
Not:
👉 “What do I personally want to say?”
That distinction changes the entire strategy.
Illustrative Case Scenarios (How Guideline M Plays Out in Real Situations)
The examples below are hypothetical scenarios based on common fact patterns seen in security clearance cases. They are designed to show how adjudicators typically evaluate risk under Guideline M—not to predict outcomes in any specific case.
Scenario 1 — Excessive Personal Browsing on Government Systems (Likely Approval)
An applicant used a government computer for excessive personal browsing during work hours.
The conduct:
- violated policy
- occurred over several months
- but did not involve prohibited or classified material
The applicant:
- acknowledged the conduct immediately
- accepted responsibility
- completed retraining
- showed no repeat behavior
👉 Likely Outcome: Approved
Why this works:
The conduct appears careless rather than malicious, and the applicant demonstrates insight and remediation.
Scenario 2 — Pornography on Government Computer (Moderate to High Risk)
An applicant repeatedly accessed pornography using a government-issued device.
The applicant initially:
- minimized the conduct
- claimed it was accidental
- denied frequency despite logs showing repeated access
👉 Likely Outcome: Significant scrutiny, possible denial
Why this creates concern:
The issue becomes judgment and credibility, not morality. Repeated policy violations combined with inconsistent explanations create substantial risk.
Scenario 3 — Unauthorized AI Tool Usage (Increasingly Serious Risk Area)
An applicant uploaded work-related material into an unauthorized AI platform to speed up workflow.
The applicant believed:
- the material was not classified
- the conduct improved efficiency
- no policy violation existed
However:
- agency policy prohibited external AI systems
- uploaded material included sensitive internal information
👉 Likely Outcome: Heavy scrutiny, depends on mitigation
Why this creates concern:
This raises cybersecurity judgment concerns and willingness-to-follow-policy concerns. Modern agencies are increasingly aggressive about unauthorized AI usage.
Scenario 4 — Improper USB Device Use (Likely Mitigable if Isolated)
An applicant used a personal USB drive on a work system to transfer files for convenience.
The conduct:
- violated policy
- was isolated
- involved no classified data
- was immediately self-reported
👉 Likely Outcome: Often mitigable
Why this works:
The applicant demonstrated transparency and immediate corrective behavior.
Scenario 5 — Repeated Cybersecurity Violations After Warnings (High Risk of Denial)
An applicant repeatedly bypassed security controls despite prior warnings from IT personnel.
The conduct included:
- unauthorized software installation
- disabling security settings
- repeated noncompliance
👉 Likely Outcome: Denied
Why this fails:
The pattern suggests intentional disregard for cybersecurity rules and poor future reliability.
Scenario 6 — Remote Work Security Mistake (Moderate Risk)
An applicant used an unsecured home network and personal cloud storage while working remotely.
The applicant:
- misunderstood policy
- cooperated fully during review
- corrected the issue immediately
👉 Likely Outcome: Depends heavily on credibility and remediation
Why this may be mitigated:
The issue appears negligent rather than malicious, and the applicant responded appropriately once aware of the concern.
Scenario 7 — Browser History Deletion After Investigation Begins (High Risk)
An applicant deleted browser history after learning that a workplace review was occurring.
Even if the underlying conduct was relatively minor:
👉 the deletion behavior created severe credibility and concealment concerns.
Likely Outcome: Significant escalation
Why this fails:
Adjudicators often interpret deletion attempts as consciousness of wrongdoing.
Scenario 8 — “Everyone Did It” Defense (Often Fails)
An applicant defended repeated policy violations by arguing:
👉 “Everyone in the office did the same thing.”
👉 Likely Outcome: Poor mitigation outcome
Why this fails:
Normalization of misconduct is not viewed as mitigation. It often reinforces concerns about judgment and willingness to follow rules.
What Actually Gets Guideline M Cases Approved
Successful Guideline M cases usually share several characteristics:
- the conduct is isolated or limited
- there is no evidence of malicious intent
- the applicant accepts responsibility
- explanations remain consistent
- there is evidence of remediation
- the applicant demonstrates understanding of the risk created
- no repeat behavior occurs
Most importantly:
👉 the adjudicator believes the conduct is unlikely to recur.
What Causes Denial Under Guideline M
Guideline M denials usually stem from:
- intentional policy circumvention
- repeated misconduct
- insider-threat concerns
- concealment or deletion behavior
- contradictory explanations
- minimizing the seriousness of the conduct
- disregard for prior warnings
- refusal to accept responsibility
Notice again:
👉 the technical violation itself is often not the deciding factor.
The deciding factor is usually:
👉 what the conduct suggests about future reliability.
Where Guideline M Cases Collapse
Most Guideline M cases do not collapse at the moment of the original conduct.
They collapse during escalation.
Stage 1 — Minor IT Violation
A policy issue occurs.
Stage 2 — Audit or Security Review
Logs or alerts identify the conduct.
Stage 3 — Initial Explanation
Applicant responds casually or inconsistently.
Stage 4 — Evidence Conflicts
Logs, timelines, or records contradict the explanation.
Stage 5 — Credibility Concerns
The issue expands beyond IT misuse into trustworthiness.
Stage 6 — Guideline E Overlap
The case now includes dishonesty or concealment concerns.
Stage 7 — Suspension / SOR
The issue hardens into formal clearance action.
👉 Final outcome: denial or revocation.
How Guideline M Interacts With Other Guidelines
Guideline M rarely exists alone.
It frequently overlaps with several other guidelines.
Guideline E — Personal Conduct
This is the most common overlap.
Once explanations become inconsistent—or concealment appears—the case often expands into:
👉 Guideline E – Personal Conduct
Guideline K — Handling Protected Information
Improper handling of sensitive systems or information may also trigger:
👉 Guideline K – Security Violations
Guideline J — Criminal Conduct
Some cases involving:
- unauthorized access
- fraud
- theft
- or illegal downloads
may overlap with:
👉 Guideline J – Criminal Conduct
👉 Once multiple guidelines apply, the mitigation burden becomes significantly heavier.
How Guideline M Appears Throughout the Security Clearance Process
Guideline M concerns can emerge at almost any point in the security clearance process.
Many applicants mistakenly assume:
👉 “If my employer handled it internally, it won’t affect my clearance.”
That assumption is often wrong.
In reality, workplace IT issues frequently migrate into the security clearance system through:
- insider-threat reporting
- cybersecurity reviews
- disciplinary records
- audit findings
- or investigator follow-up
And once the issue enters the clearance process:
👉 it takes on an entirely different level of seriousness.
The SF-86 Stage
Some Guideline M issues first surface during completion of the:
👉 SF-86 Security Clearance Form
This may happen when applicants disclose:
- disciplinary actions
- prior investigations
- terminations
- security violations
- or conduct involving computers or systems
At this stage, applicants often underestimate the importance of wording.
But the SF-86 becomes:
👉 the foundation of the investigative record.
And once explanations are written there:
👉 they are repeatedly compared against future statements.
The Investigation Stage
Guideline M issues frequently expand during the:
👉 security clearance investigation
because investigators may obtain:
- audit records
- disciplinary findings
- system logs
- cybersecurity reports
- witness statements
- insider-threat referrals
Applicants are often surprised by how detailed these records can be.
This is why guessing, minimizing, or improvising explanations becomes so dangerous.
Because investigators frequently already possess:
👉 objective technical evidence.
The Subject Interview
The
👉 security clearance subject interview
is one of the most important stages in Guideline M cases.
Investigators are evaluating:
- honesty
- consistency
- accountability
- understanding of the conduct
- and future reliability
This is where many applicants unintentionally damage their cases.
Common mistakes include:
- minimizing conduct
- blaming coworkers
- pretending not to remember obvious activity
- denying logs that already exist
- or becoming defensive
Once credibility problems emerge:
👉 the case often becomes significantly harder to mitigate.
The LOI Stage
If concerns remain unresolved, applicants may receive a:
👉 Letter of Interrogatory (LOI)
This is often where the government attempts to:
- lock in explanations
- clarify technical conduct
- compare statements against evidence
- and evaluate mitigation
This stage is extremely important because:
👉 poorly framed responses often become the basis for future allegations.
The Statement of Reasons (SOR) Stage
If the government believes serious concerns remain, the applicant may receive a:
At this point:
👉 the issue is formalized.
The government is now alleging that the conduct raises national security concerns under Guideline M—and often Guideline E as well.
This is where:
- mitigation
- credibility
- and strategic framing
become critical.
The Hearing and Appeal Stage
Some Guideline M cases proceed to:
- DOHA hearings
- written appeals
- agency review boards
At this stage, adjudicators and judges often focus heavily on:
- accountability
- insight into the conduct
- remediation
- future reliability
- and whether the applicant truly understands why the issue matters
This is why:
👉 dismissive or minimizing attitudes are so dangerous.
Learn more in:
👉 Security Clearance Hearings and DOHA Appeals
What Actually Wins Security Clearance Cases Under Guideline M
Most applicants think these cases are won by proving:
👉 “I didn’t mean any harm.”
But Guideline M cases are rarely decided that simply.
What actually wins these cases is:
👉 a record that demonstrates trustworthy future behavior.
That means:
- accepting responsibility appropriately
- providing consistent explanations
- showing remediation
- eliminating ambiguity
- demonstrating cybersecurity discipline going forward
- and making the file easy to approve
This is one of the most important concepts in the clearance system:
👉 adjudicators are not deciding whether you are a “bad person.”
They are deciding:
👉 whether they can confidently trust your judgment in the future.
That is why:
- credibility matters enormously
- minimization hurts badly
- and defensibility drives outcomes
If you want to understand how strong security clearance cases are actually built, review:
👉 How to Win a Security Clearance Case Using Proven Mitigation and Record-Control Strategies
Decision Language Explained (What These Terms Actually Mean)
Guideline M cases often contain language that sounds technical or intimidating.
Understanding these phrases gives you a strategic advantage.
“Misuse of Information Technology Systems”
This does not only mean hacking.
It includes:
👉 violations of technology, cybersecurity, or system-use rules that raise trustworthiness concerns.
“Unauthorized Access”
This does not necessarily mean criminal intrusion.
It can include:
- accessing systems beyond permission
- bypassing restrictions
- or viewing material without authorization
“Insider Threat”
This refers to someone whose conduct creates potential internal security risk.
The government evaluates whether behavior suggests:
- recklessness
- circumvention
- intentional disregard for controls
- or future vulnerability
“Intentional Circumvention”
This is one of the most dangerous phrases in Guideline M cases.
It means:
👉 the applicant knowingly bypassed rules or restrictions.
This dramatically increases adjudicative concern.
“Unresolved Concern”
This phrase drives many denials.
It means:
👉 the issue exists in the record, but the adjudicator does not believe it has been clearly resolved.
“Clearly Consistent With National Security”
This is the actual approval standard.
It means:
👉 the adjudicator feels comfortable defending approval if the case is later reviewed.
If that confidence does not exist:
👉 approval usually does not happen.
Frequently Asked Questions About Guideline M
Can pornography affect a security clearance?
Yes.
Not because of morality—but because using prohibited or inappropriate content on government or workplace systems raises concerns about judgment and rule compliance.
Can ChatGPT or AI tool usage affect my clearance?
Increasingly, yes.
Unauthorized use of AI systems involving work-related or sensitive information can create serious Guideline M concerns.
Can I lose my clearance for using a USB drive?
Potentially yes—especially if the use violated policy or involved sensitive systems or information.
What if everyone violated the same policy?
That usually does not help.
Adjudicators evaluate your conduct individually, and “everyone did it” often reinforces concerns about normalization of misconduct.
Can excessive personal browsing hurt my clearance?
Yes—particularly if it was repeated, prohibited, or involved inappropriate content.
What if I didn’t know the policy?
Lack of knowledge can sometimes mitigate a case, but repeated or obvious violations are harder to excuse.
Can deleted browser history become an issue?
Absolutely.
Deletion behavior often creates separate credibility or concealment concerns.
Can I recover from a Guideline M issue?
Often yes—especially if the conduct was isolated, non-malicious, and properly mitigated.
Why National Security Law Firm
Most law firms approach Guideline M as a technical issue.
That is a mistake.
At National Security Law Firm, our security clearance lawyers understand that Guideline M cases are actually about:
👉 judgment, reliability, cybersecurity discipline, and future trustworthiness.
Our team includes:
- former adjudicators and federal insiders
- attorneys familiar with insider-threat investigations
- national security lawyers experienced in high-risk clearance matters
We approach these cases from the perspective of:
👉 how the decision-maker will evaluate the record.
That changes everything.
Complex cases are reviewed through our internal
👉 Attorney Review Board
This means:
- multiple experienced attorneys evaluate your file
- weaknesses are identified early
- mitigation strategy is tested before submission
- and the case is structured around approval defensibility
Most clients come to us after receiving advice focused only on explanation.
But Guideline M cases are not won through explanation alone.
👉 They are won through credibility, remediation, consistency, and strategic record control.
You can read what clients say about working with our team in our
👉 4.9-star Google reviews
Related Statutes and Guidance
Explore how these rules are applied in real cases in the
👉 Security Clearance Lawyers Resource Center
If you want to go beyond the rule itself and understand how to actually win under Guideline M—how adjudicators evaluate IT misuse, what mitigation works, and how strong cases are built—review:
👉 How to Win a Security Clearance Case Using Proven Mitigation and Record-Control Strategies
Speak With a Security Clearance Lawyer Before the Record Hardens
If Guideline M is affecting your case, the most important question is not:
👉 “Was this a major IT violation?”
It is:
👉 “What does this conduct suggest about my future reliability?”
Because once these concerns are documented:
👉 they are reused
👉 re-evaluated
👉 and often expanded into broader credibility concerns
The earlier the issue is strategically addressed, the better the chance of preventing escalation into:
- suspension
- SOR
- denial
- or revocation
If you want to evaluate your situation before the record hardens against you, you can:
👉 schedule a confidential consultation with a security clearance lawyer
The Record Controls the Case.
SECURITY CLEARANCE DENIED OR REVOKED
If you are appealing a security clearance determination, it is imperative that you obtain experienced legal representation. Doing so will provide you with the best opportunity to obtain or maintain your clearance.
Click Here For a No Obligation, Always Confidential Consultation
